Programming languages such as C and C++ rely too heavily on the programmer not making memory-related mistakes, agency says [300 words].
What: NSA says organizations should consider making a strategic shift from programming languages such as C/C++ to “memory-safe” languages such as C#, Go, Java, Ruby and Swift. With these languages, memory management does not rely on the programmer adding code to implement memory protection. Rather, it is managed automatically via a combination of compile time and runtime checks.
These protections, when used with available code hardening defenses such as tool analysis, compile options and operating system configurations, can help reduce memory-usage related vulnerabilities and make it harder for threat actors to exploit them.
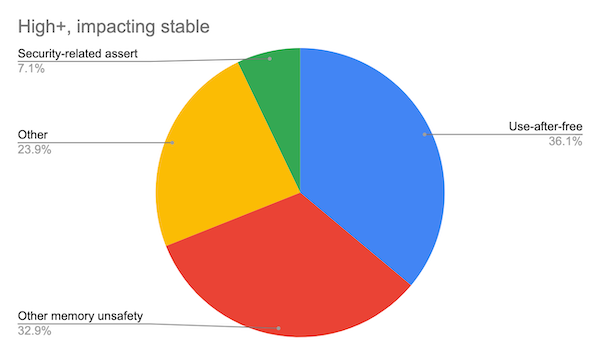
Why: Many exploitable software vulnerabilities are based on memory issues such as buffer overflow and those related to memory allocation and deallocation. Previous studies—one by Google in 2020 and another 2019 study from Microsoft—showed some 70% of exploitable vulnerabilities are memory related. Much of this stems from the fact that common languages rely on programmers to perform due diligence on memory references, the NSA said.
Software analysis tools can help detect memory management issues. But the inherent protections available with memory-safe languages can help prevent these issues from cropping up in the first place. The use of memory safe languages does not provide full protection against exploitable memory issues. But they do provide considerable protection, the NSA said.
NSA’s recommendations for non-memory safe languages:
Analyze software using SAST and DAST to identify memory use issues in software to mitigate issues where possible.
Make it difficult for threat actors to exploit memory management issues via options such as Control Flow Guard (CFG), Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP).